The internet is a staple in our society. From social interactions to financial transactions, every aspect of our existence is, in some way, connected.
While this interconnectedness brings convenience, it also presents a significant risk if not handled with care.
And that line between convenience and catastrophe is often determined by our cybersecurity measures.
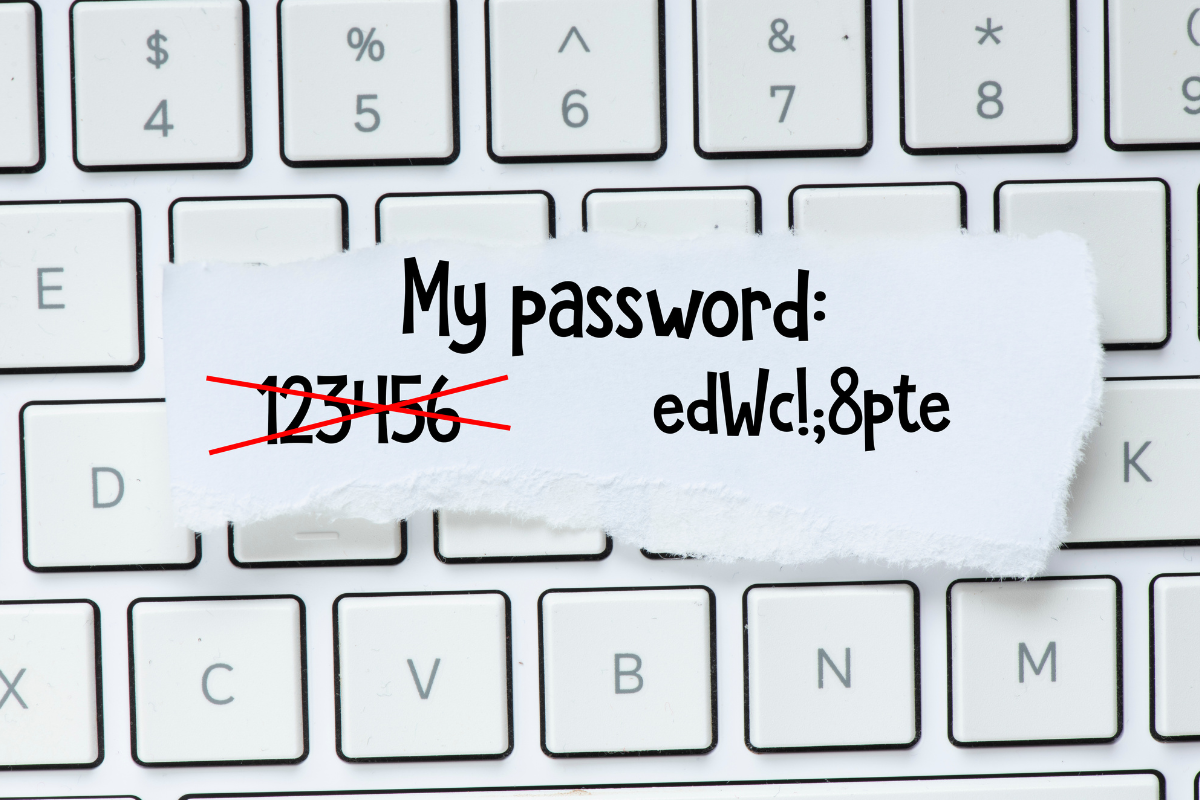
One of the most overlooked yet critical aspects of online security is the strength of our passwords.
A weak password is like leaving your front door unlocked, inviting criminals into your life with open arms.
Why Are Weak Passwords Dangerous?
A report by GoodFirms found that 30% of internet users have suffered security breaches due to weak passwords. Cybercriminals seek to invest the minimum effort required to reap maximum benefit.

Passwords are the perfect target because they’re usually easy to crack and offer unhindered access to personal and financial information.
Cybercriminals equipped with sophisticated tools can crack a simple password in seconds.
However, unauthorized access is just the start of the malicious activities hackers deploy by exploiting weak passwords.
Identity theft is a common consequence of account takeover attacks. Criminals can assume the identity of the victim, leading to financial losses, legal issues, and severe damage to one’s reputation.
Additionally, weak passwords can lead to data breaches, where vast amounts of sensitive data are exposed.
For businesses, this can result in financial losses, loss of customer trust, and even legal repercussions.
For individuals, it means personal information, including addresses, financial details, and more, is readily available for malicious actors to exploit.
Data breaches may not be dangerous only financially – individuals can experience even life-threatening acts.
The Power Of A Strong Password
A strong password is a formidable barrier between your digital life and potential intruders.
It’s the first line of defense in safeguarding your personal, financial, and sensitive information from unauthorized access.
Strong passwords generally contain a mix of letters (both uppercase and lowercase), numbers, and symbols.
You can always check online if you’re unsure whether the password you choose is strong enough.
The more complex the password, the harder it is for criminals to break through. An 8-character password of only numbers or only letters can be cracked in seconds.
On the other hand, strong passwords of 14 characters containing letters, numbers, and special characters would take years to crack.
However, the challenge for most individuals is creating and remembering these complex combinations for every online account. Let alone the one complex password – even that is difficult enough.
Password Managers To The Rescue
This is where password managers come into play. These tools are designed to generate and store complex passwords for each of your online accounts securely.
They encrypt your passwords with advanced algorithms, ensuring they are inaccessible to unauthorized users.
With a password manager, you only need to remember one master password – the key to your digital vault.
Password managers also give a boost to your security with features like password sharing (no more unsafe password-sharing on Messenger!), breach alerts, and two-factor authentication.
They take the guesswork out of password creation and management – using it ensures that each account is guarded by a unique and robust password.

Password Security Best Practices
- Assess your current passwords: Evaluate the strength of your existing passwords. If they are too simple, repetitive, or have been in use for a long time, it’s time for a change.
- Use a password manager: Adopt a reputable password manager to create, store, and manage your passwords. Ensure that your master password is strong and unique.
- Enable Two-Factor Authentication: Whenever possible, enable two-factor authentication for your online accounts. This adds an extra layer of security, requiring a second form of identification beyond just your password.
- Stay informed: Keep abreast of the latest trends in cybersecurity. Being informed is a crucial step in staying ahead of potential threats since cybercriminals discover new vulnerabilities monthly, if not more often.
Should You Regularly Update Passwords?
Security experts have long advised to update passwords every three months to maximize security.
However, federal and expert guidance has shifted, arguing that there is little benefit to changing an already strong and complex password.
Once you protect your account with a strong password, it’s best to keep it for life. If you have to change it, make sure the new password is stronger or at least just as strong as the last.
Conclusion
Using strong passwords and enabling two-factor authentication is no longer optional – it’s a necessity.
The fact that the majority of data breaches come as a result of weak passwords should be a wake-up call for internet users to start taking their digital security seriously.
While remembering different complex passwords is challenging, with tools like password managers, you have no excuse not to take action to protect your sensitive accounts.